Tech
Anon Vault: A Comprehensive Guide to Secure Digital Storage, Digital Privacy, Cybersecurity Evolution, Regulatory Compliance, Integration Strategies, and Future Innovations

Anon Vault presents a system that protects digital information by guaranteeing absolute anonymity.
Modern digital life requires the most critical protection of sensitive information than it has ever needed. The concept of an anon vault operates with three interconnected features through advanced encryption technology while it also employs decentralized storage and privacy-by-design principles. The main function of anon vault systems involves secure data storage that operates under full anonymity to shield sensitive information from unauthorized access. Businesses and individual users now adopt privacy-enhanced approaches because they maintain access together with operational functionality while fighting against evolving cyber threats.
The initial segment of this paper presents an explanation of why anon vault systems hold important value in cybersecurity practices. Modern readers gain a clear understanding of security through modern encryption techniques and decentralized systems when they learn how these components support each other. An anon vault provides users with a comprehensive defense against inside attacks which protect their data from breaches along with identity theft and privacy violations. This solution fulfills regulatory requirements which include data protection laws that apply to the US and UK territories. The anon vault operates as a preemptive solution that functions as a secure storage system for digital assets to create trust in online relationships thus serving as an indispensable tool for maintaining digital privacy.
The Evolution of Anon Vault for Secure Storage
The anon vault has seen a series of technological advances as digital privacy requirements have increased throughout the modern digital environment. Digital storage systems from the early days emphasized capabilities over security features at a time when security protection was not a priority. The development of advanced tools for cyber defense occurred because cyber threats grew more complex thus requiring protective measures with both data safety and anonymity features. Contemporary anon vault systems incorporate two key features to counter recent challenges through high‑level encryption and decentralization of their architecture which defends against single point failures.
Technology innovation gave birth to anon vault solutions which addressed the problems created by increasing data breaches alongside stricter regulatory requirements. The anon vault exists now as a multi-purpose security solution which functions well within multiple digital infrastructure setups. This innovation has gained widespread adoption by organizations operating in privacy-sensitive markets especially in the US and UK to meet their requirements under GDPR and other local data protection standards. The anon vault establishes itself as a multifunctional cybersecurity tool because encryption advancements and multi-step authentication strategies continuously develop to counter new threats.
Essential in refining the anon vault have been the technical developments together with the increased user understanding and digital expertise of its platform. People who have become aware of their online privacy needs have led to an increasing interest in security solutions which conceal personal identities alongside secure data storage. The evolution demonstrates how usability and security should exist at equal levels which the anon vault realizes through its advanced technology paired with user-friendly interfaces. The anon vault transformed from an obscure technological solution into an essential digital product that fulfills modern needs of data storage.
Anon Vault and Digital Privacy: Ensuring Continuous Confidentiality
A strong integration between a digital strategy and an effective anon vault system creates vital privacy and confidentiality protection against growing digital data breach threats. Through its design the anon vault establishes two distinct data components which prevents unauthorized persons from connecting details about users to their stored information.
Digital privacy covers more than basic storage functions because it includes multiple significant aspects. The anon vault creates an effective data protection system against risks including surveillance and data abuse since it maintains both strength and user convenience. The system implements protection at various levels that uses encryption in conjunction with rigorous permission frameworks and concealed user verification systems. Users now enjoy the ability to access data using convenient and confidential systems simultaneously. Such protection allows users to maintain their digital privacy through the anon vault during unrestricted online activity.
The anon vault earns special acceptance among privacy-oriented regions including US and UK because it matches high practicality needs with robust privacy standards. Almost all jurisdictional data protection regulations are exceeded by the capabilities of the anon vault when these standards apply to the US and UK. Through the use of this technology businesses demonstrate their dedication to protecting user privacy therefore they build strong customer trust while maintaining their position as security leaders in the digital world. Anon vault represents a system beyond storage services since it offers a comprehensive solution for digital privacy which maintains transaction confidentiality constantly.
The Technology Behind Anon Vault: Cutting‑Edge Security Infrastructure
The anon vault contains three essential security components consisting of progressive encryption procedures and distributed storage networks together with active authentication technologies which form a remarkably secure infrastructure. The encryption algorithms employed by recent anon vault systems turn sensitive data into unreadable forms which prevents even targeted interceptions from identifying the content. The security of encrypted data increases through decentralized methods that distribute content among various nodes because this decentralized approach eliminates the danger of one central point of vulnerability.
The development of the anon vault depends on modern technological advancements. The integration of blockchain technology becomes an ongoing research and engineering effort to build these systems since blockchain ensures unalterable records that provide data verification. The dual encryption and decentralization method delivers both established security tools and upcoming security concepts which maintains user protection during ongoing digital threats.
Due to its advanced technology foundation the anon vault stands well-protected against current cyber security risks. The dual advantage of this solution comes from its anonymous data protection system that still enables secure access. Digital users can use their devices without fear of data breaches because the anon vault system provides complete freedom for online activities. The solution was engineered to adjust according to organizational requirements which makes it suitable for all types of users ranging from single people to large businesses. The anon vault establishes new data security standards through its combination of advanced technology with strict security protocols that transform digital protection in dynamic environments.
Anon Vault and Regulatory Impact: Navigating Legal Requirements
The adoption of a properly executed anon vault system creates significant effects on businesses that must comply with multiple regulatory requirements. Tightening data protection legislation now forces businesses across US and UK territories to implement secure privacy‑oriented data protection solutions due to strict compliance standards. The anon vault solves these problems through its design of encrypted decentralized storage which makes businesses less vulnerable to data privacy law violations.
Digital transaction policies from regulatory organizations mandate that personal information exposure needs to be kept at a minimum. The anon vault reaches maximum security by dividing user identities from encrypted distributed data stored securely on multiple nodes. The setup meets the requirements of GDPR alongside state-specific privacy rules because PII remains inaccessible in centralized databases. Modern cybersecurity strategies now heavily depend on the anon vault because organizations need this solution to fulfill regulatory requirements.
The implementation of an anonymization vault within organizational networks brings both regulatory compliance benefits as well as decreased financial risks and increased customer loyalty. Organizations must prioritize this practice because privacy breaches often create substantial financial impacts and erosion of company reputation in current market conditions. The adoption of an anon vault enables companies to lead data privacy protection activities which results in consumer trust alongside regulatory compliance. Current legal standards find their match and exceed their requirements through the implementation of an anonymous storage solution which creates a vital tool for modern data security strategies.
An organization must implement Anon Vault as part of their total cybersecurity approach
Well-established organizations need to implement anon vault as part of their complete cyber defenses for obtaining optimal data protection. The implementation process starts with system analysis to adjust anon vault technology toward full compatibility with existing technology frameworks. The combination of traditional cybersecurity approaches with innovative anonymizing techniques through the design of an appropriate strategic framework enables the anon vault to provide stronger defense against new security threats.
The first step of establishing an anon vault requires organizations to define their specific security demands. The evaluation process of existing digital systems leads to identification of optimal storage encryption solutions. Standardized APIs and secure protocols serve to connect the anon vault to the system which promotes compatibility with all platforms. The system integration process receives backing from systematic employee training along with periodic security audit procedures to enable all stakeholders optimize their use of the tool.
The successful implementation of an integration strategy includes both scalability features and flexibility elements. Organizational needs development alongside advanced cyber threats enable the anon vault to be modified and restructured without interfering with operational business continuity. The proactive strategy both strengthens organizational security measures together with building readiness against future security challenges. When an organization incorporates the anon vault into its cybersecurity approach it establishes both trust-based operations and resilience through full protection of all its digital information.
The evaluation establishes Anon Vault as a superior alternative to conventional storage methods
Traditional storage methods have distinct differences from an anon vault technology which delivers specific distinct advantages. Data repositories used in traditional storage systems have operated in centralized facilities thus exposing all sensitive content to potential unauthorized access alongside data breach risks. The decentralized nature of the anon vault framework decreases stored information vulnerability because it deploys a decentralized approach. Digital privacy transformation involves more than technological migration because it means adopting a new philosophy for privacy security.
The anon vault enables data anonymity through advanced encryption methods as it provides users secure and flexible access to stored information. Traditional systems maintain single-point access systems yet this presents a major risk because data loss becomes a systemic failure. When data spreads across various nodes of the anon vault system attackers face increased difficulty in executing complete dataset breaches. A distributed security system remains vital for modern times since cyber attackers stay busy perfecting their attacks on centralized data systems.
The anon vault design enables innovative antiterrorist improvements of security protocols while most traditional storage systems normally do not include these updates. The shift to an anon vault provides organizations with immediate security enhancements while structuring them to face anticipated digital threats in the developing digital environment. The anon vault demonstrates superior protective capabilities than common approaches because it delivers enhanced compliance with modern privacy standards together with innovative solutions for organizations that strive to protect their sensitive data.
Future Trends in Anon Vault Technology and Innovation
Technology progress within anon vaults continues to expand promisingly because of digital world development. Through continuous research and development of encryption and distributed ledger technology together with artificial intelligence capabilities both user experience and security features of anonymized vaults are expected to improve. The anon vault plans to evolve through efforts to integrate updated risk evaluation systems with automatic encryption management and advanced ways to authenticate users while dealing with modern sophisticated cyber threats.
The anon vault will develop two major features in upcoming years according to industry experts and experts. These enhancements will focus on interface usability with more user-friendly features as well as expanded scalability to reach a larger audience. An anon vault has already gained the attention of American and UK companies because they recognize its advantages for satisfying formal regulatory obligations. Advancements in research investigations will lead to fundamental changes in how digital privacy can be maintained because demand is increasing. Additional security enhancements built by these solutions allow organizations to protect their data better while maintaining their position in front of evolving cyber threats within the dynamic digital environment.
The author predicts that the anon vault will function as the key driver behind the future of cybersecurity development. Anon vault technology will achieve higher protective capabilities as developers continue their enhancements while adding more artificial intelligence components to threat detection systems. The new developments will give users and organizations abilities to defend their digital contents with full confidence and assurance of security in a digital landscape that maintains both innovation and privacy nesta.
Conclusion: Embracing the Comprehensive Benefits of Anon Vault
The anon vault operates as a revolutionary solution which addresses current digital security needs in modern complex networks. This security solution extends maximum defense through encryption algorithms which combine decentralized file storage systems together with features protecting user privacy at the user-initiated level to fulfill today’s sophisticated data security requirements. An integration of an anon vault within digital strategies provides organizations protection against cyber threats alongside compliance with shifting regulations in both US and UK markets.
The anon vault applies a cybersecurity strategy that tackles present security needs together with features which adjust to evolving threats ahead. Any individual who wishes to achieve complete digital protection alongside resistance needs this essential security tool. Users who adopt this advanced security measure gain digital confidence to handle their information securely because the system operates with one of the most secure platforms currently in use.
FAQs on Anon Vault
What is an anon vault?
An anon vault represents a protected digital storage system with top-rated encryption together with decentralized architecture to fully conceal user data.
The data privacy features of an anon vault function through what mechanism?
Anon Vault creates multiple levels of encryption protection which uses restrictive access procedures together with information isolation techniques designed to protect privacy.
The main technologies which enable an anon vault to function include decentralization along with advanced encryption?
State-of-the-art encryption together with blockchain principles and dynamic authentication protocols make up powerful security features of Anon vaults.
An anon vault fulfills what regulatory requirements?
The system safeguards personal information by using encryption protocols to maintain standard compliance as per GDPR regulations.
The user base which can take advantage of anon vault services consists of what population?
The privacy-focused markets in US and UK value this storage solution because it provides them with safe and anonymous data storage capabilities.
Users should expect which kind of evolutions in anon vault technology will emerge in upcoming times?
Modern threat detection systems derived from AI will work together with improved scalability functions while integrating better with ongoing cybersecurity standard development.
Also Read:
Tech
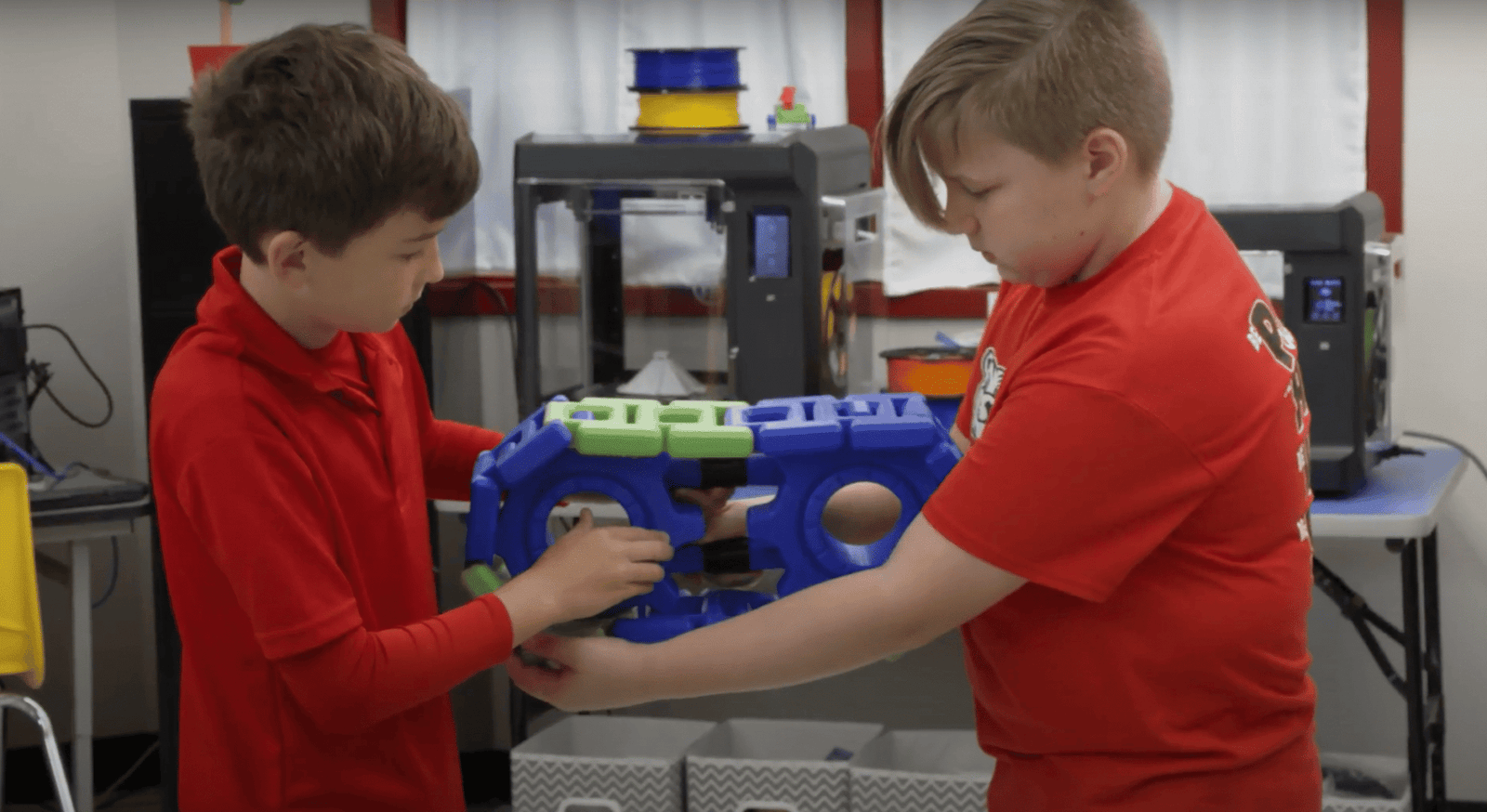
Visualizing Complexity: 3D Printing in the Modern Classroom
Education is, fundamentally, an act of translation. A teacher’s job is to take an abstract concept—a complex chemical bond, a geological formation, or a biological system—and translate it into a language that a student can grasp.
For decades, we relied on two-dimensional tools for this: textbook illustrations, whiteboard diagrams, and projector slides. While effective, these tools lack dimension. A student looking at a cross-section of a human heart on a flat page has to perform mental gymnastics to visualize how the ventricles and atria actually wrap around each other in three-dimensional space.
The introduction of the 3d printer into schools over the last decade was a massive leap forward. Suddenly, students could hold the data in their hands. Kinesthetic learners, who struggle with abstract lectures, could touch and manipulate the geometry.
However, the “first wave” of educational printing had a significant limitation: it was monochrome. A human heart printed in solid grey plastic is certainly better than a drawing, but it is still a “grey blob.” The student still has to memorize which tube is the aorta and which is the vena cava. By upgrading to the new generation of multi-filament technology, educators are removing this final barrier, turning physical models into intuitive, self-explanatory learning aids.
The Cognitive Load of Monochrome
In pedagogy, we talk a lot about “cognitive load”—the amount of working memory resources used to process information. If a student spends 50% of their mental energy just trying to figure out what they are looking at, they have less energy left to understand how it works.
A single-color 3D print often has high cognitive load. Imagine a printed model of a car engine block. In a single color, the pistons, the valves, and the casing all blend together. The student has to squint at the texture to differentiate the parts.
A multi color 3d printer solves this instantly through visual segregation. By printing the engine block in clear or grey, the pistons in metallic silver, and the valves in red, the function of the machine becomes obvious. The eye is guided immediately to the moving parts. The cognitive load drops, and the “Aha!” moment happens faster. The color isn’t decoration; it is instructional scaffolding.
The “Killer App”: Biology and Anatomy
Nowhere is this more critical than in the biology lab. Organic structures are messy. They don’t have straight lines or clear labels.
Consider the standard CPK coloring convention in chemistry, or the anatomical standards in medicine. We are trained to associate Red with oxygenated blood (arteries), Blue with deoxygenated blood (veins), Yellow with nerves, and White with bone or cartilage.
With a multi-material printer, a teacher can produce an anatomical model that adheres to these standards directly off the build plate. A printed kidney section can show the renal pyramids in pink and the collecting ducts in white. A skull model can highlight the different cranial plates in contrasting pastel colors, making the suture lines distinct.
For a medical student or a high school biology student, this is transformative. They aren’t just holding a plastic shape; they are holding a coded data set. They can trace the path of a nerve (yellow) through the foramen of a bone (white) without needing a reference key.
Geography and Topography
The utility extends to the earth sciences as well. Topographic maps are notoriously difficult for younger students to interpret. Understanding that a series of concentric lines on a map represents a steep hill is an abstract skill.
3D printing that data makes it physical. But printing it in multi-color makes it readable. A geography teacher can print a terrain model where the water level is Blue, the lowlands are Green, the mid-elevation is Brown, and the mountain peaks are White.
Suddenly, the concept of “sea level” and “elevation” is visible. Students can see the snow line. They can see how the green valley flows into the blue lake. This application is also vital for explaining geological strata. A core sample printed with distinct layers of color representing limestone, shale, and sandstone allows students to visualize the age of the earth in a way that a black-and-white diagram never could.
The Student as Creator
The benefits aren’t limited to the models the teachers make; they apply to what the students create themselves. Modern STEM education emphasizes “Design Thinking”—the process of empathy, definition, ideation, prototyping, and testing.
When students are tasked with designing a product—say, a custom game controller housing—giving them access to color adds a layer of professional design constraint. They have to decide: Which parts of this object are for gripping? Which are for display? How do I use color to tell the user how to hold it?
This forces them to think like industrial designers. They aren’t just making a shape; they are communicating intent. A student who prints a tool with a “Safety Orange” handle and a “Grey” body is demonstrating a higher level of understanding than a student who prints the whole thing in blue because that was the spool loaded in the machine.
Conclusion: From Novelty to Necessity
For a long time, 3D printers in schools were treated as novelties—machines that sat in the corner of the library printing keychains and Yoda heads. As the novelty wears off, we are focusing on utility.
We know that physical models improve learning outcomes. We know that color coding improves data retention. Combining these two facts makes the argument for multi-material printing undeniable. It bridges the gap between the digital perfection of a CAD file and the physical reality of the classroom.
By embracing this technology, we aren’t just making “prettier” models. We are giving students a clearer, brighter, and more understandable window into the complexities of the world around them. In the fight for student engagement and understanding, color is one of the most powerful tools we have.
Tech
The 150-Inch Battlefield: Are Laser Projectors Finally Ready for Hardcore Gaming?

For years, there has been a strict divide in the world of display technology. If you wanted immersion and cinematic storytelling, you bought a projector. If you wanted twitch reflexes, competitive framerates, and low latency, you bought a monitor or a high-end gaming TV.
Gamers have historically steered clear of projectors, and for good reason. In the past, connecting a console to a projector was a recipe for frustration. The input lag (the delay between pressing a button and seeing the action on screen) was often upwards of 100 milliseconds—an eternity in a First-Person Shooter (FPS) where reaction times are measured in frames. The images were often washed out, and the refresh rates were sluggish, leading to motion blur that could induce nausea during fast camera pans.
However, the arrival of laser technology has fundamentally altered this landscape. The latest generation of Ultra-Short-Throw (UST) units has bridged the gap, offering specs that don’t just rival gaming TVs but offer an experience that no 65-inch panel can touch. It is time to reconsider the projector as a legitimate weapon in a gamer’s arsenal.
The Latency Myth: Breaking the 15ms Barrier
The single most important metric for any gamer is input lag. In the competitive scene—think Call of Duty, Fortnite, or Valorant—milliseconds matter. A delay means you are dead before you even see the enemy shoot.
Traditional lamp projectors were slow because of the complex image processing required to throw an image across a room. Today’s premium laser units have optimized “Game Modes” that strip away unnecessary post-processing to prioritize speed. We are now seeing laser projectors capable of delivering input lag as low as 8ms at 1080p 120Hz, and sub-15ms at 4K 60Hz.
To put that in perspective, most casual console gamers playing on a standard living room TV are experiencing between 15ms and 30ms of lag. Laser projection has effectively caught up. The button-to-pixel response is now instantaneous enough for everything from rhythm games to fighting games, where frame-perfect timing is essential.
Immersion: The Tactical Advantage of Size
While monitors offer speed, they lack scale. Moving from a 27-inch monitor or a 55-inch TV to a 120-inch or 150-inch projection screen is not just an aesthetic upgrade; it changes how you process the game environment.
In an FPS or an open-world RPG, a massive screen fills your peripheral vision. This creates a sense of presence that VR headsets attempt to simulate, but without the bulky headgear. On a 150-inch screen, distant sniper targets that would be a few pixels wide on a TV become clearly defined objects. You can spot movement on the horizon easier simply because the visual data is physically larger.
Furthermore, a 4k laser projector delivers this size without sacrificing resolution. With next-gen consoles like the PS5 and Xbox Series X pushing native 4K textures, you need a display large enough to actually appreciate the detail. On a small screen, the intricate design of a character’s armor or the texture of distant terrain is lost; on a laser setup, it is rendered in stunning clarity.
The Return of Couch Multiplayer
One of the sadder trends in modern gaming has been the death of split-screen multiplayer. As games became graphically demanding, developers dropped local co-op. But even when games do support it (like Mario Kart or Halo), playing on a split 55-inch TV is miserable. Each player ends up squinting at a tiny quadrant of the screen.
Laser projection revives the golden era of local multiplayer. If you split a 150-inch screen into four quadrants for a Mario Kart tournament, each player gets a 75-inch diagonal display. That is larger than most people’s main TV. This scale transforms social gaming, making it viable to host LAN-party-style events in a single living room without everyone needing their own monitor.
What to Look for in a Gaming Projector
If you are ready to make the switch, you need to look beyond the basic “movie” specs. When you go to shop movie projectors, you typically look for color accuracy and contrast. For a gaming rig, you need to check for three specific features:
- Auto Low Latency Mode (ALLM): This feature, part of the HDMI 2.1 standard, allows your console to automatically tell the projector to switch into “Game Mode” the moment you launch a game. This ensures you never accidentally play with movie processing settings turned on.
- High Refresh Rates (120Hz support): While 60Hz is standard, the ability to accept a 120Hz signal (even at 1080p) is a game-changer for fluidity. It makes camera movement look buttery smooth and reduces motion blur significantly.
- MEMC Technology: Motion Estimation, Motion Compensation helps smooth out video, but for gaming, you often want the ability to turn this off or have it optimized for gaming to prevent the “soap opera effect” from interfering with gameplay precision.
The Verdict
For the professional e-sports athlete whose career depends on a 360Hz refresh rate, a desktop monitor remains the king. But for the 99% of gamers who want to be transported into the worlds of Cyberpunk 2077, Elden Ring, or Zelda, size is the ultimate immersion multiplier.
Laser projectors have finally shed the sluggish performance of their ancestors. They offer the speed required to compete and the scale required to be amazed, proving that the best window into the metaverse might just be your own living room wall.
Tech
Tech Without the Headache: Easy-to-Use Software for Seniors

Technology should make life easier—not more confusing. Yet for many seniors, modern software feels like a maze of updates, passwords, and hidden settings. The good news is that many developers now design software specifically for simplicity, accessibility, and peace of mind. Choosing the right tools can open doors to communication, entertainment, health, and independence—all without frustration. This guide explores the most intuitive software for seniors, highlighting ease of use, clarity, and built-in support.
1. Communication Made Simple: Staying Connected Without Confusion
Staying in touch with family and friends is a top priority for older adults, but complex apps and frequent redesigns often make it difficult.
Best Options:
- Skype and Zoom: These remain two of the easiest video call tools thanks to one-click join links and built-in accessibility features like captioning and screen magnification.
- GrandPad: A tablet and app system made for seniors—large icons, no passwords, and 24/7 live support.
- Jitterbug Smart4: This phone features voice navigation, a simplified interface, and a dedicated customer care line.
Tips for Success:
- Enable auto-login and contact shortcuts.
- Use voice commands to call or message without typing.
- For hard-of-hearing users, enable live captions in call settings.
2. Health and Wellness Apps That Don’t Overwhelm
Monitoring health shouldn’t require navigating endless menus. Modern senior health apps offer automation and visual clarity.
Top Picks:
- MyChart: Easy access to doctors, prescriptions, and lab results—no jargon, just straightforward buttons.
- Pill Reminder Pro: Provides large-font alerts and photo-based pill identification.
- Apple Health & Fall Detection (on iPhone): Automatically tracks steps, heart rate, and safety incidents, alerting contacts if a fall is detected.
Checklist for Ease:
- Choose apps with single-screen dashboards.
- Verify compatibility with smart devices (Apple Watch, Fitbit).
- Turn on auto-notifications for upcoming appointments or medications.
3. Entertainment Without Tech Stress
Streaming music or watching movies should feel like flipping a channel—not decoding a menu.
Best Tools:
- Netflix and YouTube (TV mode): Both provide straightforward menus, large icons, and voice search.
- Spotify “Car Mode” (available in app settings) offers oversized controls and minimal menus.
- Audible: Ideal for book lovers who prefer listening over reading.
Smart Tip: Use a smart TV remote with voice control or connect a tablet to a TV for bigger text and easy browsing.
4. Security Without the Struggle
Seniors are often targeted by scams, so intuitive security software is essential.
Recommended Solutions:
- Norton 360 Deluxe: Runs quietly in the background with minimal pop-ups.
- Bitdefender: Offers “Autopilot Mode,” automatically handling scans and updates.
- Google Password Manager: Syncs safely across devices with autofill enabled.
Quick Safety Steps:
- Use automatic updates for peace of mind.
- Turn on email phishing protection (available in most browsers).
- Consider biometric logins (face or fingerprint recognition) instead of passwords.
5. Creative Tools for Memory, Cards, and Connection
Seniors often enjoy sharing photos, cards, and memories. The right creative tools make it effortless.
Most User-Friendly Software:
- Google Photos: Automatically backs up images, organizes albums, and suggests collages.
- Hallmark Create & Print: Digital version of classic card-making—large text, drag-and-drop simplicity.
Pro Tip: Look for apps that allow offline access, ensuring seniors can enjoy them even without Wi-Fi.
6. Everyday Utility Tools That Actually Help
From reminders to navigation, these simple apps keep daily life running smoothly.
Helpful Software:
- Magnifying Glass + Flashlight (iOS/Android): Turns a phone into an easy reader for menus or receipts.
- Google Maps “Lite” Mode: Simplifies directions and labels, great for low-vision users.
- Evernote Basic: Lets users record notes or voice memos instead of typing.
Ease Checklist:
- Look for larger font settings.
- Enable voice assistance (Google Assistant, Siri).
- Choose apps with offline support for travel.
💻 FAQ: Choosing and Using Software That Works for Seniors
Choosing the right software for seniors isn’t about getting the newest app—it’s about finding tools that feel clear, predictable, and easy to recover from when something goes wrong. The best options reduce clutter, use readable text, and keep important actions obvious instead of buried in menus. This FAQ focuses on practical questions families and older adults ask most. Use these answers as a quick checklist for choosing tech that supports independence and confidence.
Q1: What makes software “senior-friendly”?
A: Clear text, contrast-friendly colors, one-tap functions, and no hidden menus. Apps that require fewer passwords and provide live help rank highest.
Q2: Are there creative tools for making printable cards or family keepsakes?
A: Yes—Adobe Express offers an easy way to make cards to print for free, perfect for birthdays, holidays, and family messages. Other tools like Hallmark’s printables also work well.
Q3: How can seniors avoid confusion when updating apps?
A: Enable automatic updates in the app store. If unsure, ask a family member or use devices with built-in support such as the GrandPad or Jitterbug.
Q4: What accessibility settings should always be turned on?
A: Text size adjustment, screen reader, color contrast, and voice commands improve usability across all devices.
Q5: Is it safe for seniors to store passwords in their browser or phone?
A: Yes, if they use encrypted managers like Google Password Manager or Apple Keychain, which are far safer than written notes or reused passwords.
Technology should empower, not intimidate. By choosing software built for clarity, seniors can connect, create, and protect themselves without needing constant help. The best programs—whether for video calls, health tracking, or creative fun—share a common trait: they remove barriers between action and satisfaction. In short, good software for seniors isn’t about complexity; it’s about comfort, confidence, and control in the digital world.
Tech
What Seattle Business Owners Need to Know Before Starting a Commercial Demolition Project

When you’re running a business in Seattle, every decision about your property matters. Whether you’re renovating a historic building in Pioneer Square, clearing land for new construction in South Lake Union, or updating an aging retail space in Ballard, commercial demolition is often the necessary first step. Yet for many business owners and property managers, the demolition process feels overwhelming. How do you find a contractor you can trust? What permits do you need? How long will it take, and what will it actually cost?
These questions are completely reasonable, especially in a city like Seattle where regulations are strict, neighborhoods are densely packed, and the weather doesn’t always cooperate. The truth is, commercial demolition is far more complex than simply tearing something down. It requires expertise, planning, precision, and a deep understanding of local codes and environmental considerations. The right demolition partner doesn’t just remove what you don’t need anymore. They set the stage for what comes next, whether that’s a complete rebuild, a tenant improvement, or a land sale.
That’s where working with an experienced local team becomes essential. Prime Demolition has built a reputation in Seattle for handling commercial demolition projects with professionalism and care. From small interior strip-outs to full building teardowns, they understand what it takes to get the job done right while keeping your project on schedule and within budget.
Why Commercial Demolition Matters More Than You Think
Most people think of demolition as the simplest part of any construction project. In reality, it’s one of the most critical phases. Poor demolition work can lead to structural damage, environmental violations, safety hazards, and costly delays. On the other hand, a well-executed demolition clears the path for everything that follows.
Consider a scenario where a property owner in Capitol Hill wants to convert an old warehouse into modern office space. Before any architect or contractor can begin their work, the interior needs to be gutted. That means removing old drywall, pulling out outdated electrical and plumbing systems, cutting through concrete floors, and hauling away tons of debris. If this phase is done carelessly, it can compromise the building’s structural integrity or leave behind hazardous materials that weren’t properly identified or removed.
Commercial demolition also involves navigating a web of permits and inspections. Seattle’s Department of Construction and Inspections has specific requirements depending on the scope of your project, the age of the building, and what materials are involved. Asbestos abatement, for example, is heavily regulated and must be handled by certified professionals. Failure to comply can result in fines, work stoppages, and even legal liability.
This is why experience matters. A demolition contractor who knows Seattle inside and out can anticipate issues before they arise, secure the right permits, coordinate with inspectors, and keep your project moving forward without surprises.
Understanding the Different Types of Commercial Demolition Services
Not all demolition projects are the same. Depending on your goals, you might need a full building teardown, a selective interior demo, or something in between. Here’s what each type of service involves and when you might need it.
Interior Demolition is one of the most common services for businesses undergoing renovations or tenant improvements. This involves stripping out everything inside a building while leaving the exterior structure intact. You might need this if you’re converting a restaurant space into a boutique fitness studio, updating an old office building, or preparing a retail location for a new tenant. Interior demolition requires precision because you’re often working around load-bearing walls, utility lines, and neighboring tenants who are still operating.
Selective Demolition takes a more surgical approach. Instead of removing everything, selective demolition targets specific areas or elements. Maybe you want to remove a section of wall to open up a floor plan, take out an old loading dock, or eliminate a mezzanine level that no longer serves a purpose. This type of work demands careful planning and skilled operators who can remove what you don’t need without damaging what you want to keep.
Full Building Demolition is exactly what it sounds like. When a structure has reached the end of its useful life or when a property owner wants to start fresh, a complete teardown is necessary. This involves bringing in heavy equipment like excavators and bulldozers, carefully dismantling the building from top to bottom, and hauling away all the debris. In Seattle, where redevelopment is happening rapidly in neighborhoods like Fremont and Georgetown, full building demolition is often the first step in transforming underutilized properties into something more valuable.
Site Preparation and Concrete Removal are critical for getting land ready for new construction. After a building comes down, there’s often a significant amount of work left to do. Concrete slabs, foundations, and underground utilities all need to be removed or capped. The site needs to be graded and compacted to create a stable base for whatever comes next. Prime Demolition has the heavy equipment and expertise to handle this phase efficiently, ensuring your site is ready for the next contractor to step in without delays.
How Prime Demolition Makes the Process Straightforward
One of the biggest concerns business owners have about demolition is the fear of the unknown. Will the project take longer than expected? Will costs spiral out of control? Will there be unexpected complications that derail everything?
Prime Demolition addresses these concerns by taking a clear, methodical approach to every project. It starts with an on-site assessment. They visit your property, evaluate the scope of work, identify potential challenges, and provide a detailed estimate. This isn’t a vague ballpark figure. It’s a comprehensive breakdown of what the project involves, how long it will take, and what it will cost.
Once you decide to move forward, they handle the permitting process. In Seattle, this can be one of the most frustrating parts of any construction project. But when you work with a contractor who knows the local requirements and has established relationships with city officials, the process becomes much smoother. Prime Demolition takes care of the paperwork, coordinates inspections, and ensures compliance with all regulations so you don’t have to.
During the actual demolition, communication is key. You’ll know what’s happening every step of the way. If an issue arises, like the discovery of unexpected hazardous materials or a structural concern, they’ll alert you immediately and propose a solution. This level of transparency builds trust and keeps projects on track.
Safety is also a top priority. Commercial demolition involves heavy machinery, falling debris, and potential exposure to hazardous materials. Prime Demolition follows strict safety protocols to protect their crew, your property, and anyone nearby. They also carry comprehensive insurance, which gives you peace of mind knowing that you’re protected if something unexpected happens.
The Advantage of Working with a Local Seattle Demolition Company
When you’re planning a commercial demolition project in Seattle, working with a local contractor offers distinct advantages. A company based in Seattle understands the unique challenges of working in this city. They know how to navigate tight downtown streets, deal with unpredictable weather, and work efficiently in neighborhoods where parking and access are limited.
Local contractors also have established relationships with city officials, inspectors, and other trades. This can make a real difference when it comes to getting permits approved quickly or coordinating with utility companies to disconnect services. They’re also more accessible. If you have a question or need to discuss a change, you’re not dealing with a national chain that treats you like a ticket number. You’re working with a team that’s invested in the local community and committed to building a strong reputation here.
Prime Demolition is a Seattle-based company that takes pride in serving local businesses. Whether your project is in the industrial heart of SoDo, the rapidly growing neighborhoods around the University District, or the established commercial corridors of West Seattle, they bring the same level of professionalism and attention to detail.
Real Results You Can Count On
The best way to evaluate any contractor is to look at their track record. Prime Demolition has completed countless commercial demolition projects across Seattle, helping businesses transform outdated properties into valuable assets. They’ve worked with property developers preparing sites for new construction, restaurant owners updating aging spaces for modern concepts, and retail landlords preparing buildings for new tenants.
Their clients consistently highlight a few key strengths. First, they deliver on their promises. When they say a project will be done in two weeks, it gets done in two weeks. When they provide a cost estimate, there are no surprise charges or hidden fees. Second, they’re problem solvers. Every demolition project comes with unexpected challenges, but their experience allows them to adapt quickly and keep things moving. Third, they’re professional and easy to work with. From the initial consultation to the final cleanup, they treat your property and your time with respect.
Common Questions Seattle Business Owners Ask About Commercial Demolition
One question that comes up frequently is how long a typical project takes. The answer depends entirely on the scope of work. A small interior demolition might take just a few days, while a full building teardown could take several weeks. Weather, permit approvals, and the complexity of the structure all play a role. A good contractor will give you a realistic timeline based on your specific situation.
Another common concern is cost. Commercial demolition pricing varies widely depending on the size of the building, the materials involved, access to the site, and disposal fees. Concrete and steel are expensive to remove. Asbestos abatement adds to the cost. The best approach is to get a detailed estimate from a reputable contractor so you know exactly what to expect.
Business owners also wonder about disruption. If you’re operating a business nearby or have tenants in adjacent spaces, you want to minimize noise, dust, and inconvenience. Experienced demolition contractors can work around your schedule, use dust control measures, and communicate with neighbors to reduce impact.
Finally, many people ask about recycling and environmental responsibility. Seattle takes waste management seriously, and so do the best demolition contractors. Materials like metal, wood, and concrete can often be recycled or repurposed rather than dumped in a landfill. This not only reduces environmental impact but can also lower disposal costs.
Taking the Next Step with Confidence
If you’re a business owner or property manager in Seattle facing a demolition project, you don’t have to figure it out alone. The right contractor will guide you through every step, handle the complexities, and deliver results you can count on.
Prime Demolition offers free consultations and project estimates. Whether you’re in the early planning stages or ready to move forward immediately, their team can assess your needs, answer your questions, and provide a clear path forward. Reach out to them today to discuss your commercial demolition project and discover how their experience and commitment to quality can make your next project a success.
Your property has potential. The first step in unlocking it is clearing away what no longer serves you. With the right demolition partner by your side, that step becomes simple, safe, and efficient.




